In the cybersecurity industry, a threat assessment is a process of examining the strengths and weaknesses of an entity's network security. It involves a risk-based analysis that assesses the likelihood and impact of threats against an organization. You can also search online risk management in network security.
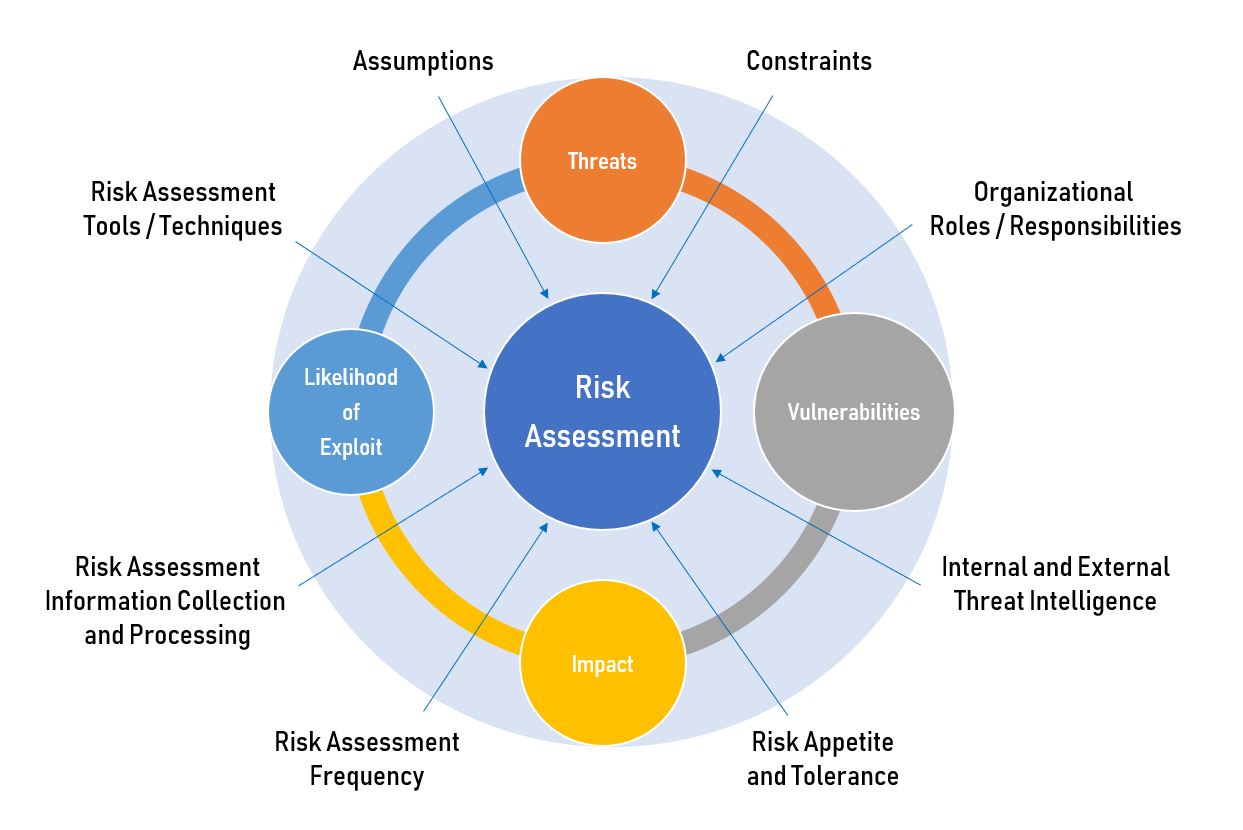
Image source: Google
There are a few steps that need to be followed in order to conduct a cybersecurity threat assessment. The first step is to identify the potential threats, both internal and external. This can be done through a variety of methods, such as conducting a vulnerability scan or evaluating threats against known targets.
Once the threats have been identified, the next step is to determine how likely they are to occur. This can be done by looking at the nature of the threat, the target audience, and other related factors. Overall, a cybersecurity threat assessment is an important step in protecting your company from potential cyberattacks.
Here are some tips to help you get started:
1. Define your business goals. What are you trying to protect? What activities do you want to prohibit?
2. Identify your organization’s vulnerabilities. There are many ways an attacker could exploit your organization’s weaknesses, both known and unknown.
3. Establish an incident response plan. How will you know if something goes wrong? How will you respond? Who will be responsible for each step of the process?
4. Conduct a vulnerability assessment. This is an overview of your organization’s security posture and identifies any areas where improvements can be made.
5. Implement proper cyber hygiene measures. These include such basics as using two-factor authentication, installing firewalls, and updating software regularly.